Mid Term Test Corrections
Test Reflection
- Question 3
- Question 5
- Question 10: Which of the following activities poses the greatest personal cybersecurity risk?
- Question 14: Which of the following is considered an unethical use of computer resources?
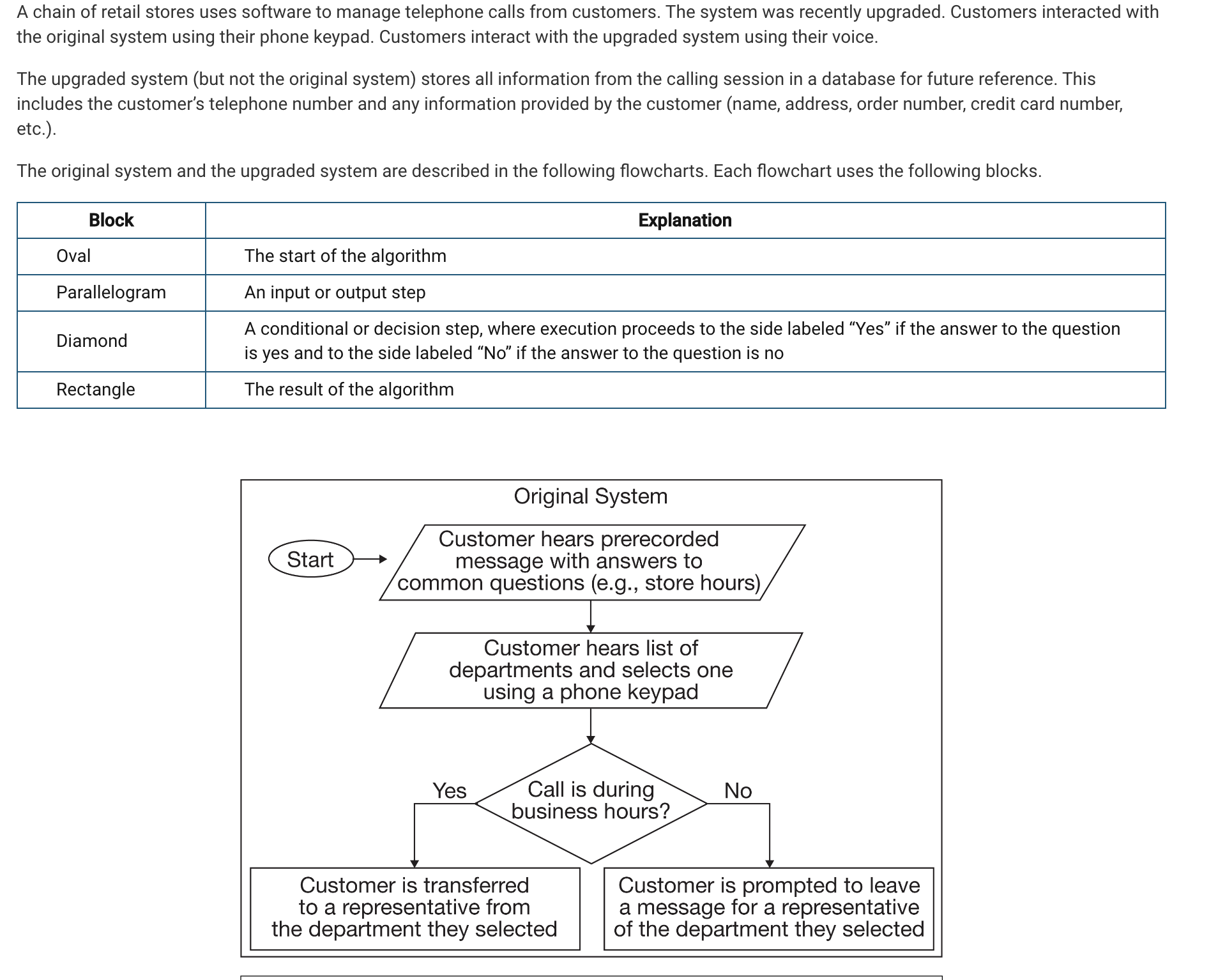
- Question 19:
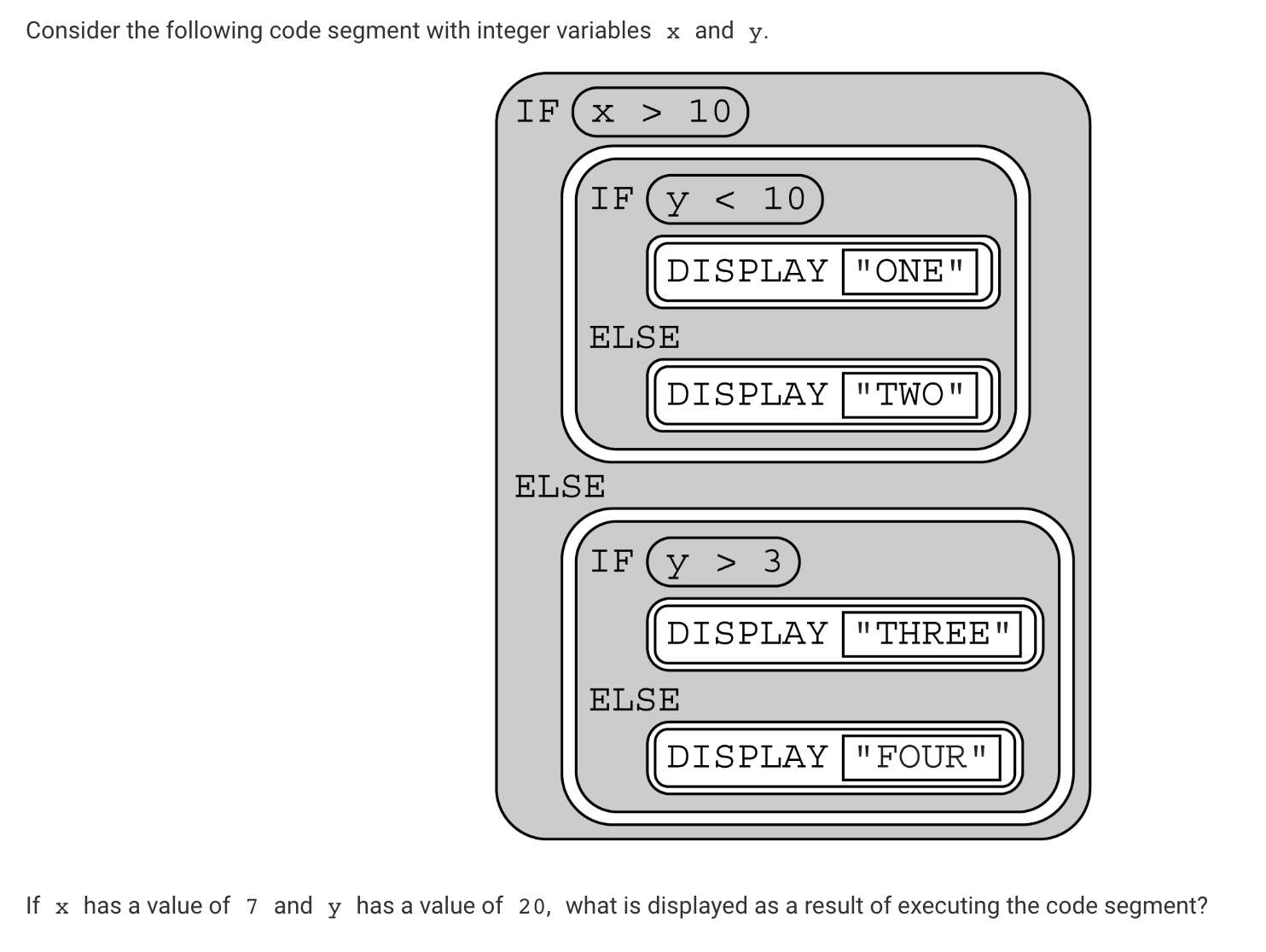
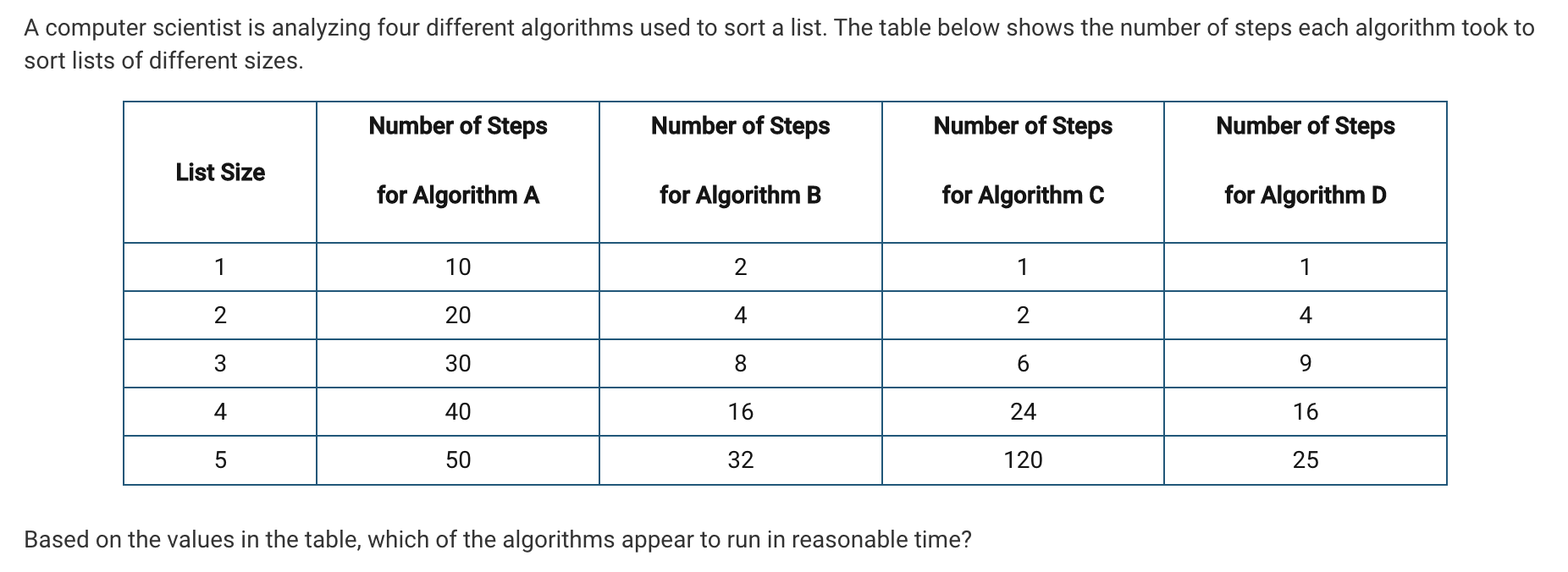
- Question 37
- Question 38
- Question 41: A large number of genetic codes are stored as binary values in a list. Which one of the following conditions must be true in order for a researcher to obtain the correct result when using a binary search algorithm to determine if a given genetic code is in the list?
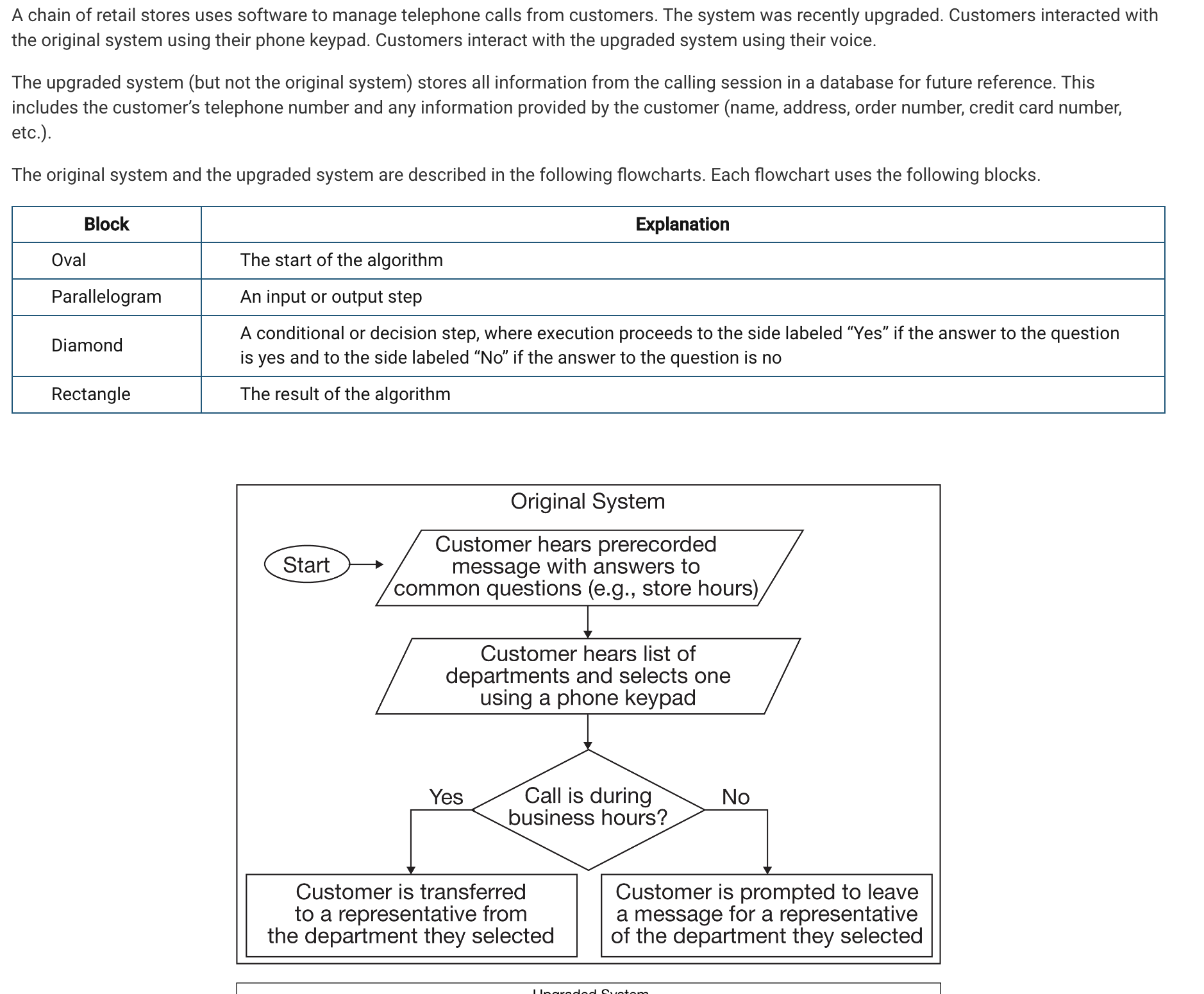
- Question 44
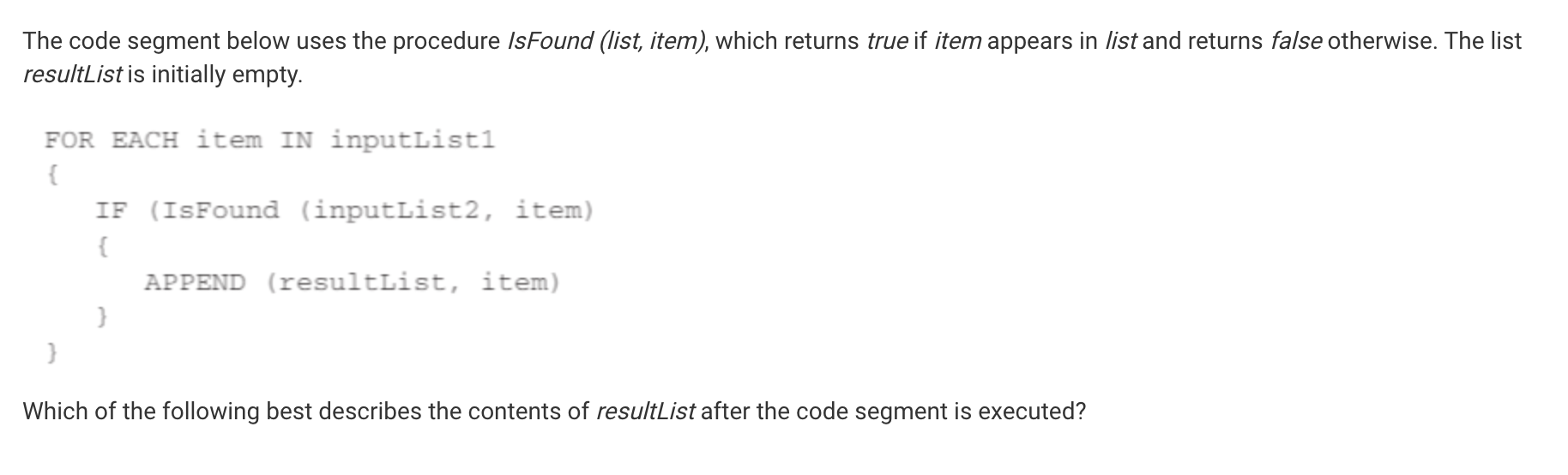
- Question 50
Question 10: Which of the following activities poses the greatest personal cybersecurity risk?
I chose A, but this is incorrect, and the correct answer is C, because sending a credit card number on email can lead to that email being intercepted and read by someone else, and them getting access to your credit card number, which is the largest security risk.
Question 14: Which of the following is considered an unethical use of computer resources?
I answered D, which is incorrect, while C is the correct answer because if you purchase a one user copy of a software, that means that only one person can use that, and if any more people use it, it is unethical and breaks that rules of the software.
Question 38
Consider the following code segment with an integer variable num.
IF(num > 0)
{
DISPLAY("positive")
}
IF(num < 0)
{
DISPLAY("negative")
}
IF(num = 0)
{
DISPLAY("zero")
}
Which of the following code segments is equivalent to the code segment above?
I chose A, when the correct answer was B, because that code segment will perform the same task as the one given.
Question 41: A large number of genetic codes are stored as binary values in a list. Which one of the following conditions must be true in order for a researcher to obtain the correct result when using a binary search algorithm to determine if a given genetic code is in the list?
I chose A, when the correct answer was B, because the list needs to be sorted based on the genetic code values because that is what a researcher is looking for.
Question 44
In the following procedure, the parameter str is a string and the parameter num is a number.
PROCEDURE printArgs(str, num)
{
DISPLAY(num)
DISPLAY(str)
DISPLAY(num)
}
Consider the following code segment.
printArgs("**", 1)
printArgs("*", 2)
What is displayed as a result of executing the code segment?